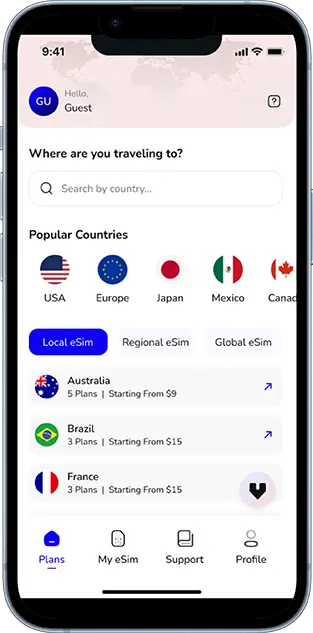
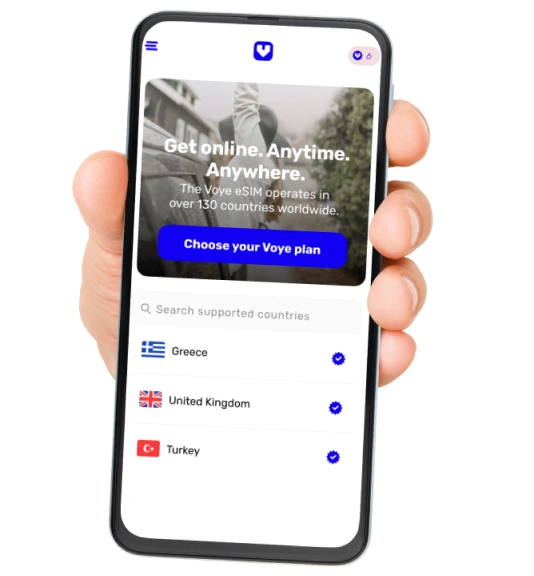
Note that iPhone devices from Mainland China aren’t eSIM compatible. Also iPhone devices from Hong Kong and Macao aren’t compatible (except for iPhone 13 Mini, iPhone 12 Mini, iPhone SE 2020 and iPhone XS)
In today’s hyper-connected world, your mobile phone number is more than just a way to make calls. It is tied to your bank accounts, social media profiles, email addresses, and even digital wallets. This makes it a prime target for cybercriminals. One of the fastest-growing threats in digital fraud is the SIM swapping scam.
SIM swapping, also known as SIM hijacking, is a sophisticated form of identity theft where attackers take control of your mobile number to gain access to sensitive accounts. With just a few pieces of personal information, scammers can bypass security systems and cause devastating financial and personal damage.
In this comprehensive guide, you will learn everything about SIM swapping scams, how they work, warning signs, prevention tips, real-world examples, and what to do if you become a victim.
What is a SIM Swapping Scam?
A SIM swapping scam is a type of fraud where a cybercriminal tricks a mobile carrier into transferring your phone number to a new SIM card that they control.
Once the transfer is complete, your phone loses network connectivity, and the scammer gains access to all calls and messages sent to your number. This includes One-Time Passwords (OTPs), which are often used for two-factor authentication.
This means attackers can reset passwords, access bank accounts, and take over social media profiles within minutes.
How Does a SIM Swap Scam Work?
Understanding the process is key to protecting yourself. Here is how SIM swapping typically happens:
1. Gathering Personal Information
Scammers begin by collecting your personal data. This may include:
- Full name
- Phone number
- Email address
- Date of birth
- Government-issued identity document
- Banking details
They often gather this information through phishing emails, fake websites, data breaches, or social media.
2. Contacting the Mobile Carrier
The attacker contacts your mobile service provider pretending to be you. They claim that:
- Your phone was lost or stolen
- Your SIM card is damaged
- You need a replacement SIM
Using the stolen personal data, they convince the carrier to issue a new SIM card.
3. SIM Activation
Once the telecom provider activates the new SIM, your original SIM gets deactivated. You suddenly lose network signal.
At this point, the scammer now controls your number.
4. Account Takeover
With access to your phone number, scammers:
- Request OTPs for banking apps
- Reset email passwords
- Access cryptocurrency wallets
- Take over social media accounts
This can lead to massive financial loss within hours.
Why SIM Swapping is So Dangerous?
SIM swapping is particularly dangerous because it bypasses traditional security systems.
- Breaks Two-Factor Authentication
Many platforms rely on SMS-based OTPs for security. SIM swapping renders this useless.
- Instant Financial Damage
Attackers can transfer money, take loans, or empty accounts quickly.
- Identity Theft
Once scammers gain control, they can impersonate you across multiple platforms.
- Difficult to Trace
These scams are often executed using fake identities and international networks, making recovery harder.
Real-Life Example of SIM Swap Fraud
Imagine you wake up one morning and notice your phone has no signal. You assume it is a network issue. Meanwhile:
- Your bank account is accessed
- Funds are transferred
- Your email password is changed
- Social media accounts are locked
By the time you realize what is happening, the damage is already done.
This scenario has happened to thousands of people worldwide, including business owners, celebrities, and even tech experts.
Common Signs of a SIM Swapping Attack
Recognizing early warning signs can help minimize damage.
1. Sudden Loss of Network Signal
If your phone suddenly shows “No Service” without reason, it could indicate a SIM swap.
2. Unusual Account Activity
- Unexpected password reset notifications
- Unauthorized transactions
- Login alerts from unknown locations
3. Inability to Access Accounts
If you are locked out of your email or banking apps, it is a red flag.
4. Receiving Suspicious Messages Beforehand
Phishing attempts or fake calls requesting personal information often precede attacks.
How SIM Swapping Scams Target Users?
SIM swap fraud has seen a rise due to increased digital adoption.
Common tactics include:
- Fake KYC update calls
- Fraudulent SMS asking to verify SIM
- Impersonation of telecom providers
- UPI-linked fraud attempts
Scammers often pose as bank officials or telecom agents to trick victims into sharing OTPs or personal data.
How to Protect Yourself from SIM Swapping Scams
Prevention is the best defense. Here are effective ways to stay safe:
1. Avoid Sharing Personal Information
Never share sensitive data over calls, messages, or emails unless verified.
2. Use Strong Authentication Methods
Prefer app-based authenticators instead of SMS-based OTPs.
Examples include:
- Google Authenticator
- Microsoft Authenticator
3. Set a SIM Lock or PIN
Most telecom providers allow you to set a SIM lock PIN that adds an extra layer of security.
4. Enable Bank Alerts
Activate transaction alerts via email and app notifications.
5. Limit Social Media Exposure
Avoid sharing personal details like your phone number, birthdate, or address publicly.
6. Regularly Monitor Your Accounts
Check bank statements and login activity frequently.
7. Contact Your Telecom Provider
Request additional security measures like:
- SIM swap verification PIN
- Account password
What to Do If You Become a Victim?
If you suspect a SIM swap attack, act immediately.
Step 1: Contact Your Telecom Provider
Report the issue and request immediate SIM deactivation.
Step 2: Inform Your Bank
Block your accounts and halt all transactions.
Step 3: Change Passwords
Update passwords for:
- Banking apps
- Social media
Use a secure device to do this.
Step 4: File a Complaint
You can report cyber fraud at:
- National Cyber Crime Portal
- Local police station
Step 5: Enable Stronger Security
Switch to non-SMS authentication methods.
Role of Telecom Companies in Preventing SIM Swap Fraud
Telecom providers play a critical role in stopping SIM swapping scams.
Key responsibilities include:
- Verifying identity before issuing replacement SIMs
- Sending alerts before SIM activation
- Implementing stricter KYC processes
- Offering SIM lock features
However, users must also remain vigilant.
SIM Swapping vs Phishing: What’s the Difference?
| Feature | SIM Swapping | Phishing |
|---|---|---|
| Method | Hijacks phone number | Tricks user into sharing info |
| Target | Telecom accounts | Emails, websites |
| Goal | Access OTPs | Steal credentials |
| Complexity | High | Medium |
Both are dangerous and often used together in coordinated attacks.
Impact of SIM Swap Scams on Businesses
Businesses are also vulnerable to SIM swapping attacks.
Risks include:
- Loss of financial assets
- Compromise of company accounts
- Data breaches
- Reputational damage
Companies must implement strong cybersecurity policies and employee awareness programs.
Future of SIM Swapping Scams
As technology evolves, so do cyber threats.
Emerging trends include:
- AI-driven social engineering
- Deepfake voice scams
- Targeted attacks on high-value individuals
This makes awareness and proactive security more important than ever.
Frequently Asked Questions (FAQs)
1. Can SIM swapping happen without OTP?
Yes, if the attacker successfully convinces the telecom provider, OTP may not be required.
2. How long does a SIM swap take?
It can happen within minutes to a few hours.
3. Can I recover money lost in a SIM swap scam?
Recovery is possible if reported quickly, but not guaranteed.
4. Is SIM swapping illegal?
Yes, it is a criminal offense under cybercrime laws.
Key Takeaways
- SIM swapping is a serious cybercrime that targets your mobile number
- It allows hackers to bypass OTP-based security
- Early detection and quick action are crucial
- Prevention includes strong authentication and awareness
Conclusion
SIM swapping scams are a growing threat in the digital age, where mobile-based transactions are widespread. The combination of social engineering and weak verification processes makes these scams highly effective.
However, with the right knowledge and precautions, you can significantly reduce your risk. Always stay alert, protect your personal information, and adopt stronger authentication methods.
Your mobile number is your digital identity. Treat it with the same level of security as your bank account.

Seamless Mobile Data Everywhere